Cyber fraud, loss of real money
The situation of cyber fraud continues to be complicated, with organized, transnational activities with increasingly sophisticated tricks, causing great damage to people and businesses, negatively affecting security and order. According to the latest survey by the National Cyber Security Association (NCA) at the end of 2024, 1 in 220 users will be a victim of online fraud, with the total estimated loss in 2024 reaching VND 18,900 billion. When falling into a scam, although 88.98% of users said they immediately warned and discussed with relatives and friends, only 45.69% of respondents said they reported to the authorities.
According to the 2024 Cyber Security Summary Report, the agency and business sector is constantly facing many serious challenges in cyberspace, especially the significant increase in the number and scale of attacks. Accordingly, up to 46.15% of agencies and businesses said they had been attacked at least once in the past year, of which 6.77% were attacked regularly. The total number of cyber attacks in the year is estimated at more than 659,000.
Many serious incidents have occurred, targeting large businesses and organizations such as state agencies, electricity, post and telecommunications, and medical and educational facilities, etc., showing that any field can be the target of cybercrime. They create sophisticated scenarios and tricks, making victims negligent, thinking that they are the ones actively looking for opportunities. And once you fall into a trap, the price to pay is not only money, but also personal information, honor and safety of yourself and your loved ones.
Countless scams
Not only stopping at traditional methods, cybercriminals today also make the most of modern technology to deceive victims more convincingly than ever.
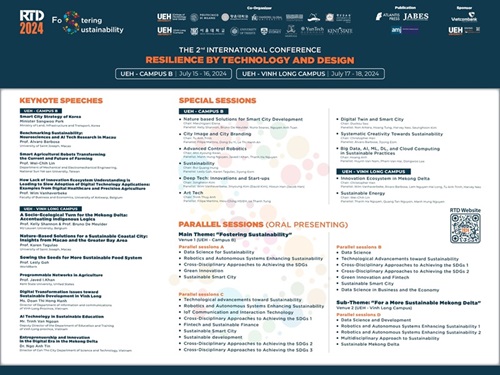
More than 20 scam tricks with trap scenarios (Source: Nhan Dan)
In general, these tricks are aimed at taking control of the phone and then appropriating property according to the following steps:
The scammers will build trust or cause confusion for the victim, asking for cooperation.
Then suggest and guide the victim to do it themselves on their personal mobile phones, downloading fake applications through the provided links.
After installation, the application will ask people to grant all permissions such as access to the phone including contacts, location, photos, camera, recording, and phone accessibility. Immediately after the application is granted permission, the subjects can monitor and completely control the victim’s phone remotely. From there, they can: compose and send SMS messages; unlock the mobile device; turn on and off the Internet, access wifi; read and write contacts; read and write call history, make calls, perform account password recovery, register for Internet Banking and Smart Banking services, change the account transaction limit, then access the victim’s account and transfer money. In addition, more dangerously, the subjects can completely collect personal information, internal information such as photos, videos, messages, phone numbers stored on the device, which poses the risk of revealing and losing State secrets (if any) and privacy. In 2025, NCA predicts that the tricks will develop unpredictably, because we will continue to witness the explosion of new technologies such as artificial intelligence (AI), blockchain technology, quantum computing such as:
Using Deepfake artificial intelligence technology: Using AI to create videos, fake voices of relatives, celebrities, etc.
Using specialized telecommunications software: making mass calls, appearing with phone numbers similar to police agencies, banks or reputable organizations, causing many people to lose their guard.
Taking advantage of security vulnerabilities on devices such as security cameras, smart locks, children’s locator watches to steal data or perform blackmail.
Application-based attacks (APT) on organizations through low-level personnel: Using phishing emails or internal impersonation to infiltrate corporate systems through human vulnerabilities, then taking control, stealing or encrypting data.
Under the cover of technology, many victims, although alert, still do not realize that they are facing fake content that they trust. By the time they discover it, their money has been lost, their personal information has been exploited, and the criminals are hiding in the digital world – invisible and difficult to trace.
High-tech crimes are becoming more and more sophisticated (Source: National Cyber Security Association)
How to protect yourself from digital dangers?
Under the pressure of increasingly sophisticated and unpredictable scams, each individual needs to become the “first shield” to protect themselves. Cyber security is not only the responsibility of the authorities, but also the ability to survive in the digital age.
If you are a student, exposure to high technology and updated information about scams is no longer strange. But because of that familiarity, sometimes subjectively and unintentionally, your data